Cybersecurity frameworks help you achieve better cybersecurity by serving as a collection of best practices, standards, and guidelines. They are built by experts to help organizations reduce risk and remain resilient. A framework helps you identify the current state of an organization’s cybersecurity program and subsequently provides the necessary information to build an improvement roadmap. Because there are so many cybersecurity frameworks to choose from, we decided to narrow down the universe to the top 5 we feel are the most valuable and well-respected. This list is obviously subjective but most of the frameworks included are household names in the world of cybersecurity.
Many organizations utilize cybersecurity framework to achieve specific cybersecurity requirements and standards, which will vary by industry. For example, the energy sector has the NERC CIP standards, and the medical industry has HIPAA. If you’re interested in the history of cybersecurity frameworks, we’d recommend listening to our presentation:
To achieve cybersecurity compliance, organizations often take advantage of integrated risk management platforms, which contain a catalog of various frameworks.
In our humble opinion, the top 5 cybersecurity frameworks are:
Selecting the best cybersecurity framework for your organization requires you to make a few considerations first:
- The maturity of your current cyber risk security program
- Your company policies and goals
- Any regulation requirements you must comply with
Overall, your team should take time to understand the universe of different cybersecurity frameworks beyond the five we list in this article, so that you can select one (or multiple) that best suits your business needs
Two Types: Maturity Models and Control Frameworks
It’s essential to understand the difference between maturity models and control frameworks. Both are frequently used to bolster cybersecurity at governments and companies and sometimes are called frameworks interchangeably.
In this article we use the term framework interchangeably in our top 5 list for the sake of simplicity. However, it’s important for you to note which ones are indeed maturity models. We will make this distinction for clarity’s sake.
So, what’s the difference between a cybersecurity framework and a cybersecurity maturity model?
Maturity models such as the popular Cybersecurity Capability Maturity Model (C2M2) from the U.S. Department of Energy help determine how well you are doing something. They are typically developed in collaboration by experts of different backgrounds who can help ensure the model considers organizations of different sizes and abilities. Maturity models take a continuous improvement approach that helps determine what improvement looks like. They have become more broadly accepted over time in both small and large organizations.
When companies and governments adopt maturity models, it drastically improves the odds of creating a cultural shift. As you get up to 2020 and 2022, there is a tacit and full acceptance that maturity concepts of institutionalization are becoming the way that security culture is created.
On the other hand, control frameworks such as the popular NIST Cybersecurity Framework (NIST CSF) are explicitly outcome-driven and help you assess whether you perform specific actions. This means organizations generally have flexibility in implementing the practices as long as they achieve ideal outcomes.
This list of top 5 cybersecurity frameworks will allow your organization to achieve a more cyber resilient program.
1. NIST CSF
The NIST Cybersecurity Framework is highly 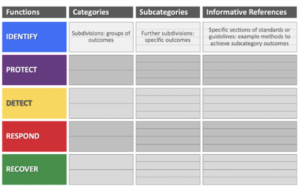 popular and has a reputation for objectivity and fairness. This framework core is made up of five functions and each function is broken down into categories and subcategories. The NIST CSF is useful for organizations of all sizes and industries. It’s outcome-driven, giving organizations the flexibility when it comes to implementation of practices. The NIST framework has easy to understand language, allowing team members that are not in the cyber or IT space to understand and use it. Its brevity allows it to be business-friendly which contributes to its widespread adoption. NIST CSF can easily integrate with a variety of other standards including NIST 800-53, ISO 27001 and more. There are resources that map NIST CSF to these standards and guidelines. All these benefits contributed to NIST CSF making our list of top cybersecurity frameworks.
popular and has a reputation for objectivity and fairness. This framework core is made up of five functions and each function is broken down into categories and subcategories. The NIST CSF is useful for organizations of all sizes and industries. It’s outcome-driven, giving organizations the flexibility when it comes to implementation of practices. The NIST framework has easy to understand language, allowing team members that are not in the cyber or IT space to understand and use it. Its brevity allows it to be business-friendly which contributes to its widespread adoption. NIST CSF can easily integrate with a variety of other standards including NIST 800-53, ISO 27001 and more. There are resources that map NIST CSF to these standards and guidelines. All these benefits contributed to NIST CSF making our list of top cybersecurity frameworks.
Get NIST CSF Free Tool
https://learn.axio.com/free-tool
NIST CSF Resource Library
The members of the Axio team have been closely involved in the development of the NIST CSF from day one and have compiled a list of recommended reading materials they have authored for our community.
NIST CSF Top Highlights
Axio’s list of the top 10 things to understand about the NIST CSF, from the team involved in its ideation. Learn more about NIST Cybersecurity Framework here.
Understanding NIST CSF Functions
Learn about the important distinction of NIST Cybersecurity Framework (NIST CSF) functions and shows how they can be the utilized to optimize your cybersecurity program.
NIST CSF to Develop Secure and Resilient Federal Information Systems
We break down how informative reference, NIST SP 800-53 controls, can be valuable for interpreting the NIST CSF.
Using NIST CSF for Compliance for Power and Utilities
The newly released mapping from NERC CIP to NIST CSF is a useful tool for those organizations within the electric power and utility industry that must adhere to NERC CIP compliance.
Why NIST CSF Helps Hospitals and Healthcare Systems
The healthcare industry is becoming increasingly vulnerable to cybersecurity frameworks and can use NIST CSF to improve their resilience and cyber posture.
NIST CSF to Build a Privacy Foundation
The flexibility of the NIST CSF extends to building a privacy foundation you can document and improve upon.
NIT CSF Secures Remote Work
Remote work has created and increased attack surface. We compile how to leverage the NIST CSF to ensure your organization stays secure working remotely.
Informative References for NIST CSF
Because the internet did not have a complete index of informative references for NIST CSF, Axio staff decided to create it here.
Considerations for NIST
https://axio.com/insights/considerations-for-starting-a-nist-csf-assessment/
Important considerations to get started on your NIST CSF assessment journey.
NIST CSF Implementation Checklist
Learn what tools you should consider accelerating your NIST CSF framework implementation.
2. CIS 20
The Center for Internet Security has a set of 20 critical security controls that outline best practices for internet security and cyber threats. These 20 critical security controls are broken down into three buckets – basic, foundational and organizational. The CIS 20 is acclaimed by many to be one of the best cybersecurity frameworks. According to a TripWire article “A study of the previous release found that by adopting just the first five controls, 85 percent of attacks can be prevented”. These best practices empower organizations to push past compliance and holistically secure their organization. One of the biggest benefits of CIS20 is that it helps users easily prioritize. The controls in the basic bucket are the most critical and have high payoff. These controls are your starting point to enabling risk reduction.
3. ISO/IEC 27001
The International Organization for Standardization and International Electrotechnical Commission developed the ISO/IEC 27001 and it’s one of the most vastly used security controls frameworks. According to Gartner’s Guide to Information Security Controls Frameworks, more than a third of organizations use the ISO/IEC 27001 as their primary regulatory framework. Organizations of all sizes and industries can become certified in ISO/IEC 27001 by an external auditor. This framework consists of 11 clauses and an Annex that provides guidelines to controls that can be implemented. Like some of the other frameworks on this list, it can be integrated with other frameworks. And due to its widespread use, there’s a variety of resources that can inform and guide users.
4. C2M2
The Cybersecurity Capability Maturity Model has 10 domains, and within each domain are approach and management objectives. The approach objectives outline what needs to be implemented and the management objectives outline how well these cybersecurity activities are implemented. Each activity within the objectives are broken down into 3 maturity levels. In order to get to the next maturity level, they must complete all activities in the previous level. The C2M2 framework is a thorough and comprehensive framework that gives a holistic view of an organization’s cyber risk management. Authors created the C2M2 for those in the electricity and oil/natural gas sector, but it can be used by any company. It’s a robust cyber risk assessment that helps you improve your organization’s cyber resilience.
Axio staff has written a comprehensive article providing a more detailed overview of C2M2
The article covers:
- Cybersecurity Capability Maturity Model (C2M2) Background
- C2M2’s Maturity Model Elements
- Components of the C2M2
- Who can benefit from C2M2
5. CMMC
Structured into 17 domains with 5 levels of certification within each domain and 171 technical practices, CMMC empowers a “collaborative risk management approach” to secure your organization. Moreover, CMMC not only prepares organizations for cyber events but also helps develop a route to recovery for when a cyber-attack unfolds. Similar to C2M2, to get to the next maturity level/certification, all the practices within the previous maturity level must be implemented. Government defense contractors use CMMC to not only protect their organizations, but also national security.
Preparing for Cyber Recovery
The use of cybersecurity frameworks can allow organizations to go beyond compliance and secure their infrastructure and confidential information. When it comes to cybersecurity it’s not a matter of “if” a cyber event occurs, it’s about “when”. With more cyber threats than ever, these best practices can decrease organizations’ susceptibility and help them develop a path to recovery when a cyber-attack is successful. The increase in cyber risks has led to the discussion of more government regulations and security requirements. For example, due to the rise in cyber-attacks from China, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) encouraged organizations to implement a number of mitigation strategies. The current cyber best practices may become security requirements in the future. By utilizing these frameworks, you can get ahead of the game.
Why No Single Framework Can Provide the Ultimate Solution?
In practice, building the most optimal security system requires more than one framework. The irony is that there is no single framework that does it all. As cyber attacks are getting more sophisticated, risk management requires a more comprehensive and enhanced defense mechanism.
Compliance Frameworks vs. Maturity Frameworks
Frameworks designed for compliance remain focused on ensuring your organization is following the regulatory mandates. In many scenarios, an approach designed for compliance alone proves to be inadequate against advanced threats.
On the opposite end of the spectrum, frameworks designed for maturity evaluate how effectively an organization is achieving a particular goal, the successfully implemented security controls and the ones that need work, and what gaps need to be bridged to realize the ultimate outcome. They provide an objective assessment of an organization’s cyber risk profile – where an organization stands in terms of its cyber security and the maturity of its control implementations, systems, and information risk management processes. Ultimately it enlightens companies on how they can improve their risk management to enhance their overall cyber security posture.
As can be seen, each framework has its merits and demerits and cannot fulfill all requirements. The best solution is to structure your framework with a holistic approach. Using both, the cybersecurity frameworks for compliance and maturity can offer an integrated score that takes into account the complete picture. Reporting the integrated score to all stakeholders including senior management and board members will help them see the overall effectiveness of your organization’s security protocols in tackling cyber threats.
Making These Top Cybersecurity Assessments Work for You
Our platform, Axio360 supports a number of the frameworks mentioned above including CMMC, C2M2, CIS20, and NIST CSF. Our NIST CSF assessment includes mappings to ISO 27001 and a number of other standards such as the NIST 800-53, COBIT, NERC CIP, and more. Using Axio360 to assess your organization will allow you to identify weak points. With that knowledge, your team will be able to address vulnerabilities by implementing controls or buying insurance. Axio360 makes it easy to pinpoint your cyber risk management gaps and roadmap towards your target. Having a roadmap and understanding your current cyber risk vulnerabilities will decrease susceptibility and build up capability to recover. Our Kanban road-mapping tool makes planning easy, adjustable and collaborative. Moreover, our milestone feature tracks progress and improvement, while our target profile feature allows for goal setting across the organization. Bring all of these top cybersecurity assessments to life with a single tool – the Axio360.

To learn more about cybersecurity assessments, read our recent blog.




