Use NIST CSF to build a privacy foundation in your cybersecurity program and facilitate compliance with CCPA and GDPR
The NIST Cybersecurity Framework (NIST CSF) provides a good foundation of security controls for achieving privacy objectives, such as those required to comply with the California Consumer Privacy Act (CCPA) or the General Data Protection Regulation (GDPR)—the two regulations that set a new, higher standard for privacy.
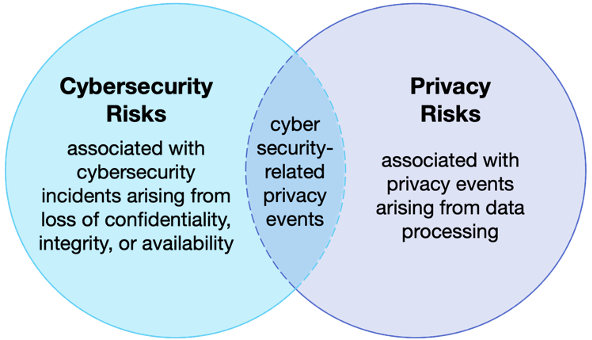
Privacy and security are close cousins. According to NIST, “Organizations cannot have effective privacy without a basic foundation of information security. Privacy is more than security, however, and includes, for example, the principles of transparency, notice, and choice” [NIST SP 800-53 r4 pg. J-1]. Considering privacy as a key objective to be enabled by your cybersecurity program is a good practice.
Relationship between Cybersecurity Risks and Privacy Risks [NIST Privacy Framework]
So how do we use NIST CSF to build a cybersecurity foundation for our privacy program? NIST CSF contains 5 Functions, 23 Categories, and 108 Subcategories; reinterpreting all of them here would make for a lengthy post. Let’s start with the first two Functions, Identify and Protect, which will provide us with a majority of the Subcategories we should consider for reinterpreting with a privacy lens.
NIST CSF Identify Function
CCPA and GDPR have provisions that allow a consumer to know what kind of information is being collected and who it is being sold or transferred to, along with other provisions, such as a right to be forgotten (i.e., have the data deleted). All of this would require your organization to know exactly what private information you have, who that private information belongs to, where it is stored and processed, what third parties have access to it, how the information will be used, et cetera.
In other words, to answer these questions, you will have needed to identify your assets (systems, software, and private information), your business environment (why you collect the information and what you do with it), and your supply chain (who you transfer or sell that information to).
Using a privacy lens and a bit of extra work, we can shift the objective of a Category into something relevant to a strong privacy program. Here are a few examples:
| NIST CSF Subcategory | Cybersecurity Interpretation | Privacy Interpretation |
| ID.AM-1 | What are the physical assets in my environment? (Who owns them? Where are they located? What are they connected to?) | What physical assets store or transact private information? (Who owns them? Where are they located? What are they connected to?) |
| ID.AM-6 | What are the cybersecurity roles and responsibilities in my organization, my suppliers, and my partners? | What are the privacy roles and responsibilities in my organization, my suppliers, and my partners? |
Interpreting NIST CST Subcategories for Privacy Compliance
The other categories in the Identify Function operate similarly. For example, Business Environment (ID.BE) shifts slightly to add privacy context as part of identifying the organization’s mission, objectives, and critical services. Governance (ID.GV) shifts to identify the organization’s policies, processes, and procedures that protect private information, along with the related regulatory, legal, risk, and operational requirements. In Supply Chain (ID.SC), refocus subcategories from cyber supply chain risk to privacy risk in outsourced data processing.
NIST CSF Protect Function
As stated earlier, the foundation of a mature privacy program relies upon strong security controls to protect the private information being collected, processed, and stored. The GDPR expects your company to define an “adequate level of data protection” and “appropriate technical or organizational measures” needed to protect the private information in your custody. The CCPA provides for direct lawsuits if non-encrypted and non-redacted information is breached as a result of the business’s lack of sufficient security controls and practices.
Each of the Categories under the Protect Function change very little when looking at them in the context of protecting private information. Implementing strong security controls as discussed in Identity Management, Authentication and Access Control (PR.AC), Awareness and Training (PR.AT), Data Security (PR.DS), Information Protection Processes and Procedures (PR.IP), Maintenance (PR.MA), and Protective Technology (PR.PT) is essential toward exercising due care for the protection of private information in your custody.
What about the other NIST CSF Functions?
While we haven’t discussed them here, the Detect, Respond, and Recover Functions aren’t to be ignored. Detection, response, and recovery are essential for your organization to remain resilient; however, the differences between a cybersecurity and privacy focus for these Subcategories is less significant; the controls and activities would largely be identical.
Where else should I look for privacy best practices?
NIST CSF is an excellent resource for building the cybersecurity foundation for your privacy program. There are many privacy-specific best practices that are not found in the NIST CSF. While your cybersecurity team leverages NIST CSF to shore up the cybersecurity foundation for your privacy program, your privacy team may want to explore additional guidance, such as the v1.0, which uses the familiar organizing structure from NIST CSF and applies it to the unique requirements of a privacy program. Similar to the NIST CSF, the NIST Privacy Framework is organized into a core (Functions, Categories, and Subcategories), profiles, and implementation tiers. Read previous Axio insights for tips in understanding how the NIST CSF is laid out. NIST has also created a crosswalk between the CSF and Privacy Framework that helps organizations understand the interrelationship between Subcategories in each framework.
About the author: Brendan J. Fitzpatrick is a Director of Cyber Risk Engineering at Axio.