In 2013 the Obama administration issued Executive Order 13636 setting forth the task of incentivizing organizations in the United States to adopt the NIST Cybersecurity Framework (CSF). EO 13636 suggested various types of incentives to promote adoption of the CSF, such as cybersecurity insurance, grants, liability limitations, streamlined regulations, public recognition, and rate recovery for price–regulated industries.
Balancing Incentivization and Independence
As of 2020, the United States government is still working to figure out the best approach to balance the serious nature of cyber threats facing our nation while respecting private industry’s independence from direct government intervention.
Cyber insurance, one of the incentives suggested in EO 13636, has seen exponential adoption since 2013. This is likely due to the similar exponential growth in cyber attacks against US businesses that have resulted in financial losses that would be covered by such insurance. There is no evidence that the increased adoption of cyber insurance is driven by the adoption of CSF. It is possible that organizations that have adopted CSF and made meaningful improvements to their cybersecurity posture are getting better rates on such insurance as a result.
The other proposed incentives have been lacking without central federal guidance. Recently the Department of Homeland Security created the Critical Infrastructure Cyber Community (C3) Voluntary Program in a bid to facilitate cooperation and communication among organizations across the country while also encouraging widespread adoption of the NIST CSF. The catch? There are still no concrete incentives being offered or any programs identified to implement the different areas of EO 13636. Even with DHS’s C3 Voluntary Program, the name gives away the continuing struggle in that the federal government has yet to put together a solid and concentrated program to incent the adoption of a cybersecurity framework that would streamline risk management and cyber resilience efforts on a nationwide level.
This is not for a lack of trying. As the cyber threat to US critical infrastructure grows from a host of malicious actors, there are positive signs from industry and the federal government. Recommended incentives were recently put forth by FERC in a white paper prioritizing transmission incentives for utilities that invested in cybersecurity, but not based solely on arbitrary investments, instead focusing on effectiveness of the investment and assigning a Return of Effectiveness (ROE). This was just a recommendation as of June 2020 and is undergoing staff comment to determine the best method to support this approach.
Shifting Recommendations to Reality Beyond 2020
The world has quickly shifted to a new paradigm of work (remote and hybrid environments). The complexity of an expanded attack surface has already lent itself to sophisticated cyber-attacks, steadily increasing both in damages and frequency. But we are just in the beginning of this transition of risk exposure. As these events gain more publicity, it will be very challenging to deny the need to understand the nature of an entity’s cyber risk exposure and plan for both addressing and alleviating the potential damages it may incur. Cybersecurity frameworks have been around for a while, but will begin to gain increasing public attention as the necessary starting point to make the complexity of cybersecurity management more effective. NIST CSF benefits from having broad and favorable brand recognition and mind share. Many C-suites and Boards of Directors have latched on to the familiar Identify-Protect-Detect-Respond-Recover mantra from the NIST CSF Functions.
We are in the early stages of this shift, but corporate liability for cyber incidents is beginning to be expanded to the CEO and Board of Directors. The Equifax shareholder class-action lawsuit is quickly setting a precedent. Providing incentives to the decision makers who drive how cybersecurity is managed may just be the necessary tipping point to move the EO 13636 recommendations to reality.
The hope is that more and more organizations will adopt a cybersecurity framework such as NIST CSF as they see the benefit from other organizations who are already using it. Such adoption could be additionally bolstered if the federal government were to establish clear incentives for critical infrastructure companies. The development of incentives should reward companies that are proactively and effectively addressing the rapidly increasing cyber threat facing the United States and protecting the critical infrastructure on which the American people depend.
Getting Started
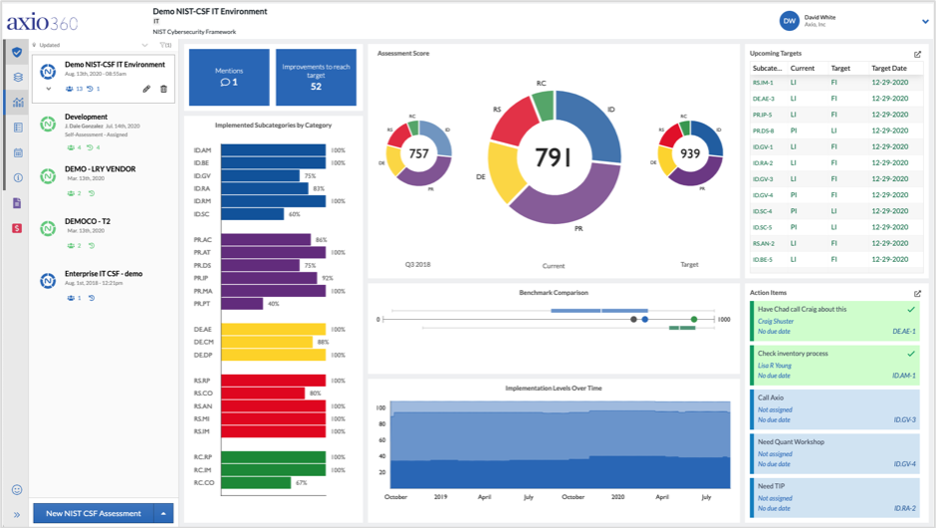
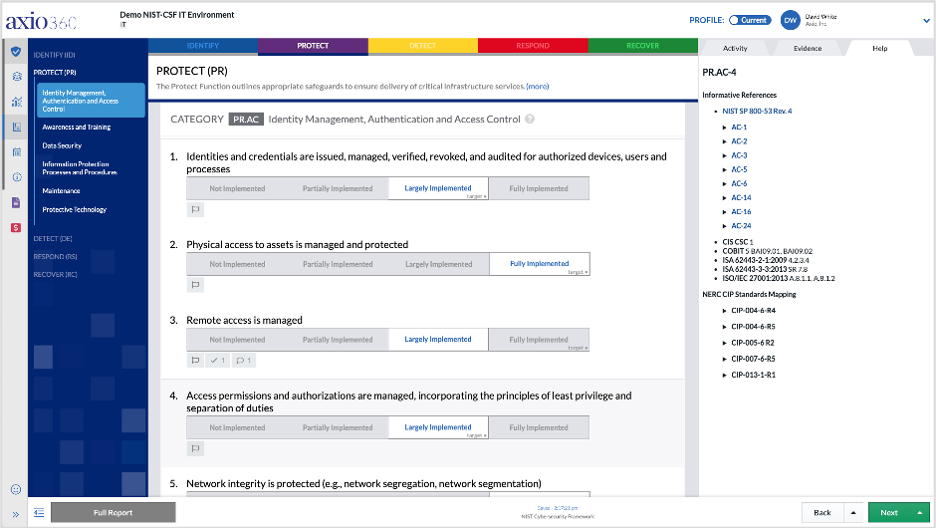
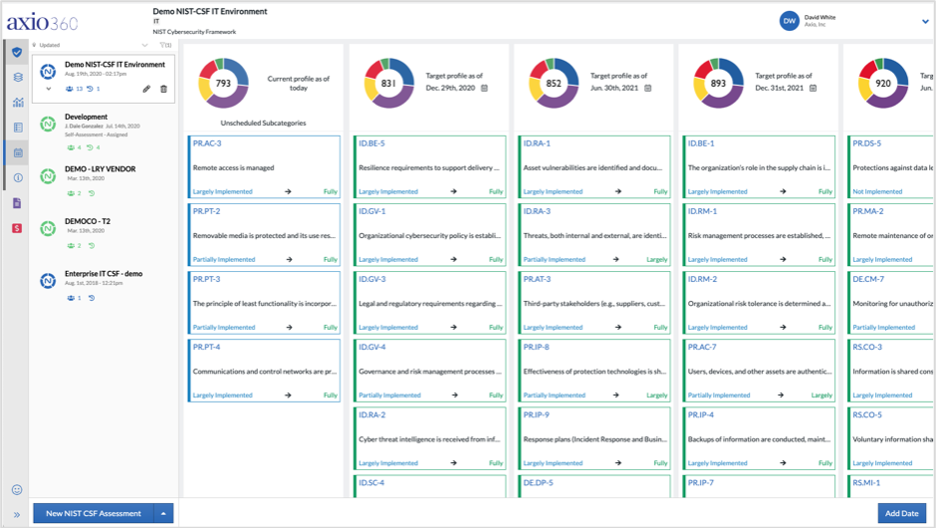
For those who want to get started in adopting a cybersecurity framework, you can begin today with Axio360.
The Axio360 platform is the easiest and fastest way to get started with NIST CSF. With the considerations above, you are well on your way to optimizing your work-from-home cyber program. If you’d like to learn more information and dive into more detail on how to perform a NIST CSF assessment in Axio360, you can book a demo and speak with one of our experts.
Concerned about remote cyber risk?
Axio’s Top 50 NIST CSF Tips to Address Remote Work Cyber Risk




