Cybersecurity Programs Benefit from a Risk-Based Mindset
Earlier in the year, we released a series of blog posts about understanding the relationship between cybersecurity and insurance. Covid-19 was the best biological example for the necessity to prepare for low probability but high impact events. Our blog series used this parallel to draw attention to the digital world and its malicious (and also sometimes careless) actors.
Digital cybersecurity events once considered unlikely and infrequent, are now on the top of everyone’s mind. These types of cyber risk scenarios are the ones worth being prepared for and have been increasingly part of the executive conversation. Given the recent Microsoft breach, it’s become increasingly evident that no amount of defense will protect and defend an organization. You need to be prepared to mitigate and manage cyber risk financially.
Insurance is becoming an increasingly important part of the equation because it speaks to the risks one can transfer outside of technological controls. However, if you are ready to purchase insurance for cyber, the landscape is much different going into 2021.
Cyber Insurance Is No Longer Profitable for Underwriters
In the past two decades, cyber-specific policy underwriting was an extremely profitable enterprise. Margins were often twice as high as traditional property and casualty policies, providing a steady cash flow for the underwriter. From the late 1990s to the present, hundreds of cybersecurity insurance policies were created to serve this market opportunity.
The wheel of fortune turned in 2020 for both the insured and insurer. It might have been the first year insurers lost money on their cybersecurity policies, according to industry insiders. The coronavirus essentially created a global work-from-home dynamic that lured cybercriminals to strike with never-before-seen intensity. The schemes were creative, opportunistic, and malicious, taking advantage of the public’s desire for new information about the disease as well as the urgent need to provide critical care to the most vulnerable.
In a time when supplies and resources were most limited, the US experienced
a 400% increase in cybersecurity incidents, according to the FBI. Many of the attacks were ransomware events that successfully halted business operations. In one tragic case, a patient could not be serviced by the nearest hospital and died in the ambulance while being transferred.
These kinds of outcomes are making cyber risk, front and center of the conversation while making insurers rethink how they want to protect an exposure that is now becoming more and more probable.
And When Nobody Thought the Year Could Get Worse, Enter SolarWinds
In regards to probability, the threat landscape came to a climax in December 2020 with the SolarWinds supply chain compromise. The nature of the cyber-attack received global attention and dominated the technology news airwaves for several weeks. It was the type of low probability/high impact digital risk we discussed in our previous blogs, amplified to global proportions.
SolarWinds impacted multiple branches of US government agencies on such a wide scale that knowledge of the scope of the attack is changing every single day. Because of the complexity of the cybersecurity incident, the repercussions of SolarWinds will most likely impact the broader insurance portfolio of affected parties’ physical assets and infrastructure for years to come. Questions are looming about whether there will be insurance coverage or not. Will it be considered an act of war or espionage? In our previous post we talked about exclusions for cyber war, and this will become more and more necessary when thinking about how to transfer future cyber risk that may materialize.
Beyond a standalone cybersecurity insurance policy, enterprises are now beginning to realize they need to look at their entire insurance portfolio to see if potentially affected assets will be covered.
The alleged “nation state” hackers responsible for SolarWinds crisis, entered over 250,000 organizations. The mechanism of the attack it its simplest form exposed vulnerabilities that impacted an intricate web of third parties. What will the financial impact be long term? Nobody knows for certain.
These same affected enterprises are now rushing to simulate similar types of attacks and even pen test their supplier’s software, as well as extend their log retention cycles. Most importantly, from a program management perspective, they are moving towards requirements for continuous security assessments.
The inherent risk in the supply chain will never go away. The enterprise must understand exactly how much it has to lose, and how the risk can be transferred through controls that are beyond technical, but also financial. Once again, this means the entire insurance portfolio must be analyzed.
So how do you map your coverage against your risk exposure in financial terms? It only takes 3 easy steps in the Axio360 platform.
Step 1: Quantify the Cyber Risk Scenarios Pertinent to Your Business in Dollar Terms
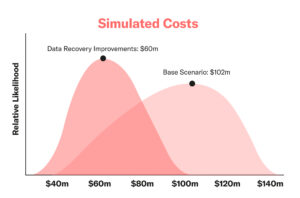
The Axio360 platform is powered by the fastest quantification method on the market today to give you a financial view of your expected exposure per scenario from the worst case to the best-case impact. You can build a model in a few hours as opposed to the traditional six months using other cyber risk quantification software that requires a long process of implementation necessitating PhDs, statisticians, and a team of consultants.
Step 2: Aggregate All Your Insurance in One Place and Scan for Potential Exclusions Using Machine Learning
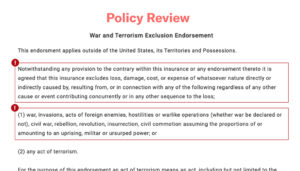
The Axio360 platform can rapidly identify problematic policy language indicating a lack of coverage.
Step 3: Align Your Insurance Gaps with Your Quantified Risk Scenarios

The Axio analyst team can assess recovery potential based on your insurance policies, contracts, and compliance with cybersecurity standards. This type of personal support ensures that you are truly insured for cyber risk in the most cost-effective and secure manner possible.
Microsoft Breach, A Use Case for a Risk Based Approach to Cyber
In the past few weeks, the Microsoft Breach further highlighted that the hackers will be successful in accessing one’s systems. You can’t stop them with a defense mindset. Was this event also sponsored by a nation state? Another act of war that may be excluded from your insurance coverage? There’s great uncertainty at the moment.
If there’s ever a time to take a risk-based approach to cybersecurity, it’s now. We envision the insurance industry to change in the coming years to think about cybersecurity in a more thoughtful and careful methodology.
Below are a few of our predictions.
Technology and AI in Underwriting
Insurers are already reassessing their policies to account for the dramatic increase in cybersecurity incidents such as ransomware and supply chain attacks.
Brokers are now reporting that premiums will be going up by as much as 20%.1 But this is only the beginning.
We envision that insurance brokers will be using more tools to better understand the nature of cyber risk for their particular clients, such as
- The ability to upload policies into an AI engine to scan for exclusions
- Rapidly search for exclusions and clauses, such as “acts of war”
- Understand their clients particular risk exposure in dollars and cents and identify gaps in the insurance policy coverage as they pertain to limits.
Insurers Will Offer Proactive Cybersecurity Services
We envision 2021 to be the aha moment in cyber risk mentality, the turning point when underwriters will be cautious in how they actualize new policy types for sale, with specific covenants in place in order for the policy holder to be reimbursed if an incident is realized. In general, the underwriter will desire to have more visibility into the insured’s real-time cyber posture, enabling a more constructive feedback loop.
Longer term, we envision underwriters to become more hands-on, with access to the insured client’s network, similar to a Managed Services Provider. This allows much faster reaction to risk in real time, as well as the ability to adjust premiums based on the strength of one’s cyber posture over a given time frame.
If you’re interested in learning how to begin the continuous cyber posture improvement journey, we welcome you to try our free assessment tool that includes 3 assessments: NIST CSF, C2M2, and Ransomware Preparedness. This is an immersive experience that is much easier and more efficient than using a spreadsheet.
Closing Thoughts
The connection between insurance and cybersecurity is more relevant now than ever before.
We hope you found this blog series insightful. To summarize, here are the three takeaways:
- You need to look at your entire insurance portfolio
- You need to quantify your cyber risk
- You need to match your analyzed portfolio to your particular exposure
This 3-step process is available in the Axio360 platform, and you can get started today.
Contact us for a personalized demo of the solution at [email protected] or book a meeting below.
1. https://www.advisenltd.com/global-insurance-prices-rise-for-12th- consecutive-quarter/